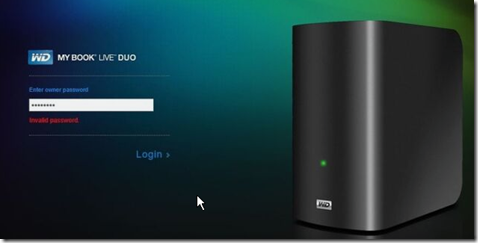
If you own a Western Digital MyBook Live NAS drive, a vulnerability is allowing hackers to access the device remotely with admin/root privileges. As per WD’s forums, users are complaining that the hackers have erased all their data after performing a factory reset on the device.
MyBook NAS devices are popular with consumers and small businesses. You can connect the device to a LAN cable and then access it or administer it via the WAN IP or Western Digital’s cloud portal. According to NIST a WizCase security researcher reported the flaw as far back as 2018.
A statement from Western Digital read:
Western Digital has determined that some My Book Live devices are being compromised by malicious software. In some cases, this compromise has led to a factory reset that appears to erase all data on the device. The My Book Live device received its final firmware update in 2015. We understand that our customers’ data is very important. At this time, we recommend you disconnect your My Book Live from the Internet to protect your data on the device. We are actively investigating and we will provide updates to this thread when they are available.
This event brings to light two important security best practices. The first is that a NAS is not a good replacement for a properly configured file server with a managed backup. NAS devices are good as backup storage, not as primary storage.
The second is that IoT devices in general, when used in businesses, should be set up by a professional and connected to a DMZ (guest zone), especially if the device is being made accessible via the Internet or through a cloud-based gateway. Since many IoT devices run a Linux operating system under the skin, a hacker that gets root access into such a device has a powerful OS platform inside the network from where to conduct reconnaisance, packet sniffing, brute force attacks or the installation of malware. In small businesses with no IT management proactively monitoring CVE’s, IoT devices are an Achille’s heel when connected inside a single-zone network segment.
Many consumer NAS devices include a plethora of freeware application programs that can be easily installed via an app store. When connected to the Internet, both the NAS’ Web interface and the installed applications increase the security footprint of the device. Internet facing/accessible devices and the applications they have installed need to be monitored for CVE’s (common vulnerability exposure) and updated. Devices with known CVE’s where no updates are available due to end-of-life or lack of vendor support, should be disconnected.