 A USB keystroke logger is a physical device that connects between your computer’s USB port and the keyboard’s USB connector. USB keystroke loggers can store several weeks worth of keystrokes for the purpose of covert surveillance and credential theft. They are commonly used by spouses trying to catch unfaithful partners, and by organizational insiders wanting to steal credentials or sensitive information.
A USB keystroke logger is a physical device that connects between your computer’s USB port and the keyboard’s USB connector. USB keystroke loggers can store several weeks worth of keystrokes for the purpose of covert surveillance and credential theft. They are commonly used by spouses trying to catch unfaithful partners, and by organizational insiders wanting to steal credentials or sensitive information.
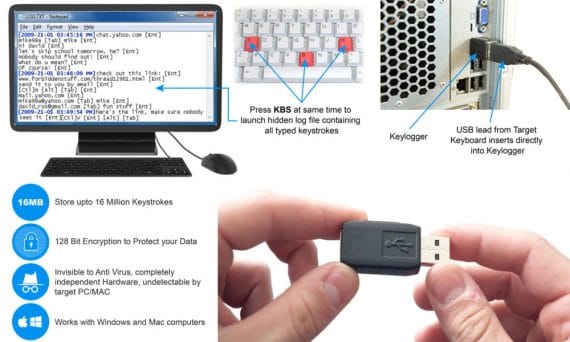
USB keystroke loggers work by taking input from the computer’s keyboard, copying it to memory, then forwarding the input to the computer. Since keystroke loggers are hardware based and have no installed drivers or software on the computer, they are undetectable by anti-malware and other security programs. Keystroke logging devices can also be embedded in specialized keyboards. If your keyboard suddenly changes for no reason, make sure to notify your IT department.
The following people are high risk to have keystroke loggers installed:
- C-Level executives with access sensitive data.
- Scientists, researchers and others with access to intellectual property.
- Accounting personnel and others with access to financial accounts.
- HR managers with access to personally identifiable information (PII).
- Health care workers with access to patient records (PHI).
- Government contractors with access to classified documents.
- IT personnel with high level access to IT resources.
USB keystroke loggers can be easily purchased on-line for as little as $ 35.00. Like many hacking tools, USB keystroke loggers straddle the line of legality. Unless proper notification is provided, recording or monitoring another person’s computer activity is not legal. Keep in mind however, that hackers are not now known for their law-abiding tendencies.
The only way to know that your PC has a USB keystroke logger is by physically inspecting it. For this reason, employees with high level access to information should lock their office doors when they leave the office and periodically check their computers visually.
