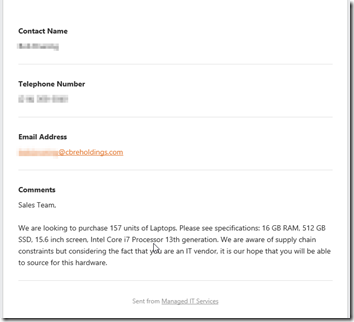
In the example below, I received a Web site lead from a person interested in purchasing laptops. Here is how I was able to quickly determine that this was fraud. I omitted the person’s name in the image because it’s very likely that that person is a real employee of the organization.
The first clue that this fraud is the ‘too good to be true’ red flag. Although we are not resellers of hardware, I would imagine that businesses that do resell hardware would love to capture an opportunity to sell a large number of units such as this.
next, a quick Internet Web page search reveals that the real organization’s URL is different than the one in the email address domain. The fraudster simply added the word ‘holding’ and purchased the new domain name.
It’s not unusual for hackers to buy similar sounding domain names of well-recognized and trusted organizations in order to masquerade as authorized buyers, finance personnel or C-level executives of the organization. This is done in order to trick people into believing that they are dealing with the organization directly.
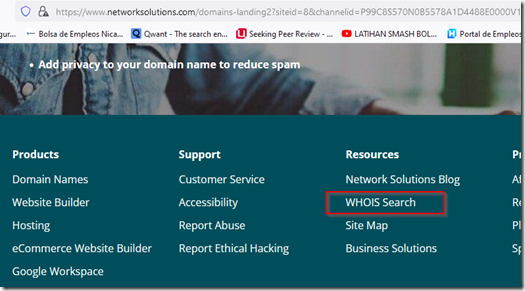
According to Wikipedia, WHOIS is a query and response protocol that is used for querying databases that store an Internet resource’s registered users or assignees. These resources include domain names, IP address blocks and autonomous systems, but it is also used for a wider range of other information. You can access WHOIS from any registrar, such as Godaddy or Network Solutions. registrars are required to provide a conspicuous link to a WHOIS search. You can usually find the link at the bottom of the registrar’s home page.
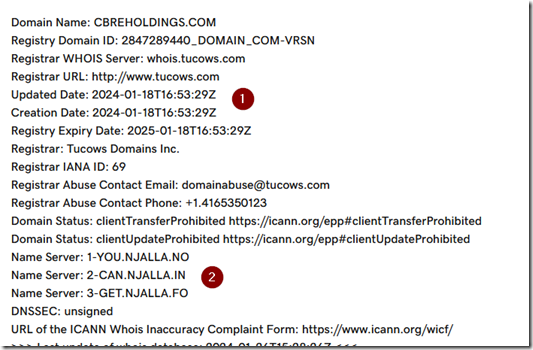
After entering the domain name in the WHOIS and performing a search, I found some interesting information that further indicated that the sales lead was fraudulent in nature.
1. The domain was purchased January 18, 2024, just a few days before I received the sales lead, another indication that it’s fake. A Wikipedia search shows CBRE holdings being established in 1906, it’s unlikely that they just realized that they needed a Web presence.
2. The DNS servers are located outside the USA, highly unusual for an organization based here.
The WHOIS results will show an email address where you can report fraud, spam and other forms of domain name abuse.